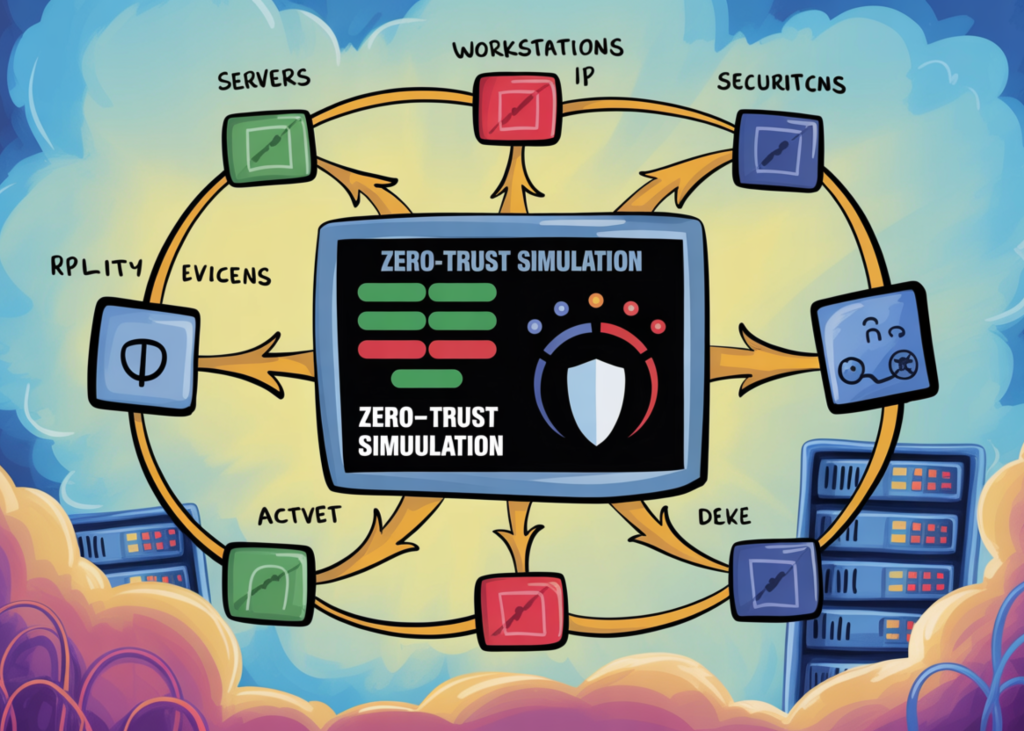
How to Build a Dynamic Zero-Trust Network Simulation with Graph-Based Micro-Segmentation, Adaptive Policy Engine, and Insider Threat Detection
In this tutorial, we build a realistic Zero-Trust network simulation by modeling a micro-segmented environment as a directed graph. We force every request to earn access through continuous verification, implementing a dynamic policy engine that blends ABAC-style permissions with device posture, MFA, path reachability, zone sensitivity, and live risk signals such as anomaly and data-volume indicators.
We then operationalize the model through a Flask API and run mixed traffic, including insider-lateral movement and exfiltration attempts. This allows us to show how trust scoring, adaptive controls, and automated quarantines block malicious flows in real time.
Setting Up the Environment
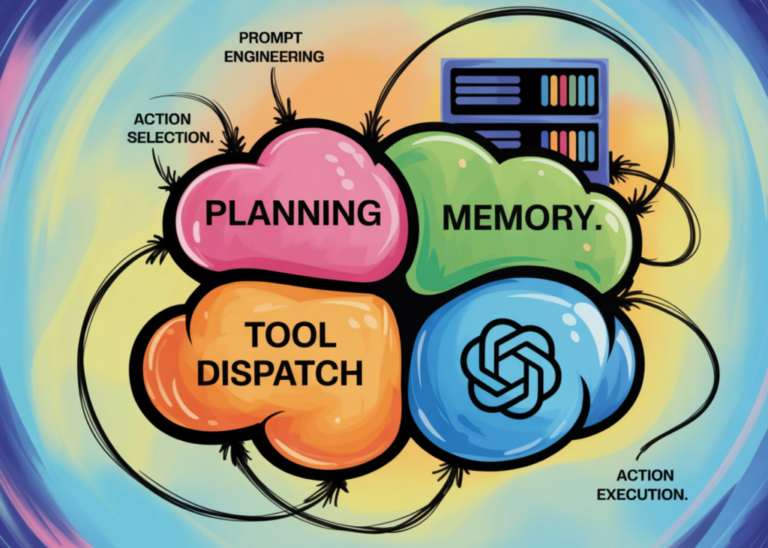
- We set up the environment by installing required libraries and importing all dependencies needed for graph modeling, risk scoring, and API handling. We define utility functions for trust normalization, hashing, timestamping, and weighted sampling to support deterministic simulations. We prepare helper functions that simplify logging and structured output formatting throughout the tutorial.
Defining Core Domain Schema
- We define the core domain schema including zones, assets, roles, device types, and contextual signals that shape our Zero-Trust environment. We formalize request, decision, principal, device, and flow record structures using dataclasses to maintain clarity and state integrity. This enables continuous trust evaluation across identities, devices, and network paths.
Constructing the Microsegmented Graph
- We construct a micro-segmented directed network graph where zones and assets are explicitly modeled with sensitivity attributes. We programmatically generate inter-zone and service-level communication paths to simulate realistic enterprise traffic patterns. We visualize the network topology to clearly observe segmentation boundaries and potential lateral movement routes.
Implementing the Zero-Trust Policy Engine
- We implement a dynamic policy engine that blends ABAC-style permissions with device posture, MFA, path reachability, zone sensitivity, and live risk signals such as anomaly and data-volume indicators. We then operationalize this model through a Flask API.
Key Takeaways
- The tutorial demonstrates how to build a dynamic Zero-Trust network simulation using graph-based micro-segmentation.
- We show how to implement a dynamic policy engine that blends ABAC-style permissions with device posture, MFA, path reachability, zone sensitivity, and live risk signals such as anomaly and data-volume indicators.
- By running mixed traffic through the simulated network, we demonstrate how trust scoring, adaptive controls, and automated quarantines block malicious flows in real time.
Note: The implementation details for the build_microsegmented_graph function have been omitted as they are part of a larger codebase. For a comprehensive understanding, please refer to the full tutorial or code repository.
The Zero-Trust Policy Engine is designed to handle requests and make decisions based on principal information, device state, and contextual signals like network context, behavior anomaly, data volume, and risk score.
Originally published at marktechpost.com. Curated by AI Maestro.
Stay ahead of AI. Get the most important stories delivered to your inbox — no spam, no noise.